Fake Play Store app promised free Netflix and sent WhatsApp link to spread
Program that circumvented the Google store filter requested access to notifications to reply to messages. It was taken down after a security company alert.
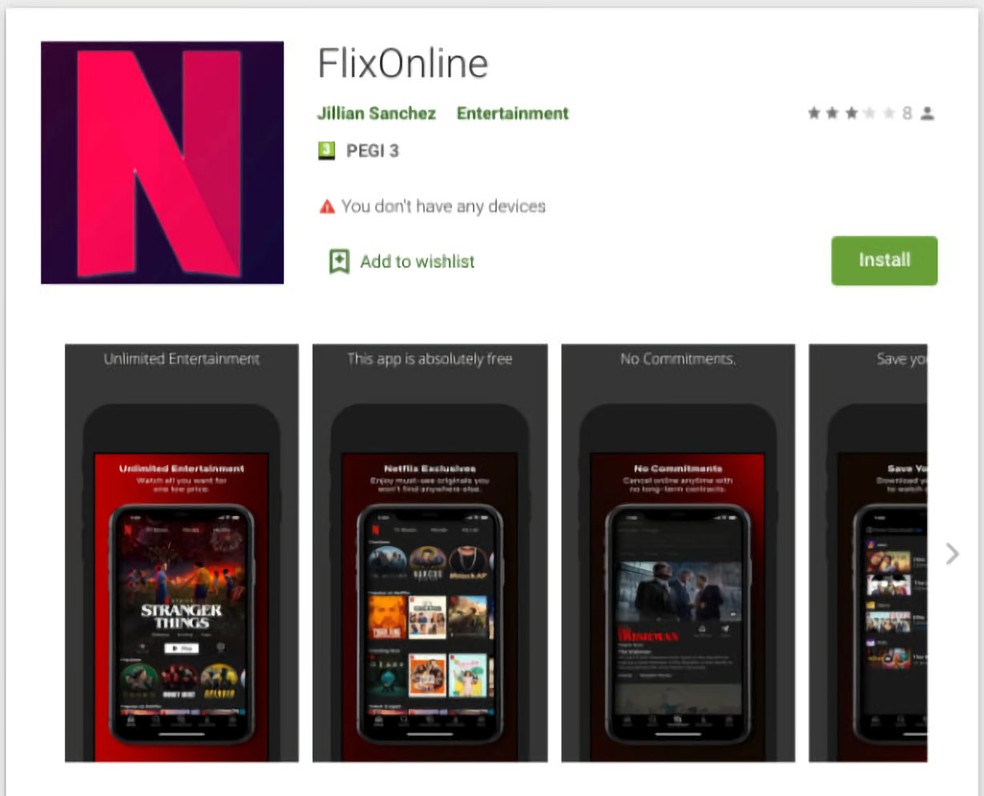
Security company Check Point said it found a fake app on the Play Store, Google’s app store, which promised 60 days of free access to Netflix content.
Called “FlixOnline”, the program caught the attention of experts for having the ability to respond to messages received by WhatsApp with links that propagated the fake content to more victims.
The reply, sent in English only, cited the coronavirus pandemic as a supposed justification for the false promotion of two months of free access.
Even with this bait, the publicity campaign was not very successful and reached only 500 downloads in the Play Store in two months.
In addition to using an icon very similar to Netflix, the app requested special permission to read notifications – something unusual for legitimate programs, but very frequent in malicious apps.
As WhatsApp notifications arrive with a button to “reply” to the message, the fake app could do this, interacting with the notification itself even without having any direct access to WhatsApp itself.
After being installed and activated – by reading notifications and turning off battery optimization – the app removed its own icon from the app drawer, making it difficult to uninstall.
Even with these characteristics, the application managed to pass through the Play Store filter, which, according to Google, has human review. After being notified by Check Point, Google removed “FlixOnline” from the store.
First time on the Play Store
The trick of responding to messages by the notification is identical to that used by a fake app found in January, which promised a free Huawei cell phone to propagate a link on WhatsApp.
The first app, however, was not on the Play Store. The Android system usually blocks the installation of apps outside the Google store, which makes it difficult to spread with fake websites.
“FlixOnline” therefore marks the first time that an app is found on the Play Store with this behavior.
Check Point experts have also warned that, with access to notifications, scammers can obtain sensitive data from users. But, apart from the ability to self-propagate, the application had no malicious actions in its logical functioning.
Although it is not known exactly what the app creator’s goal was, the absence of more aggressive malicious code may have helped “FlixOnline” to pass through the Play Store filters.
As a general recommendation, users should only enable the reading of notifications for highly trusted applications. In newer versions of Android, the system itself has a feature to access the notification history, eliminating the use of apps for this purpose.